Silicon IP Cores
KEXP
AES Key Expander
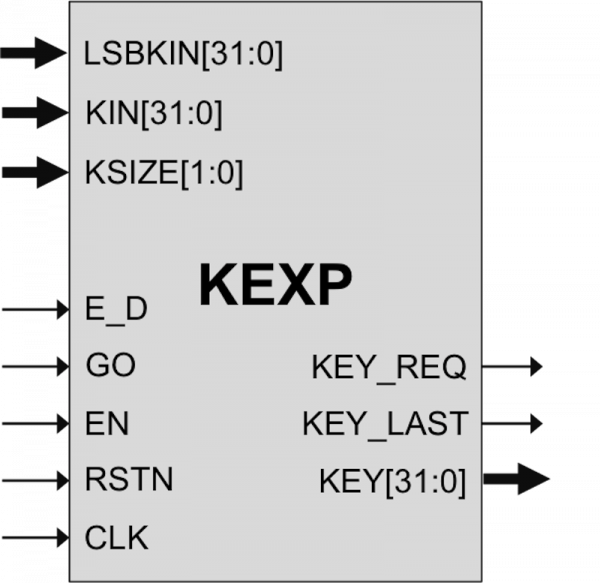
The KEXP IP core performs AES key expansion, and is an option for the AES, AES-P, AES-CCM and AES-GCM cores. It processes 128-bit blocks, and is programmable for 128-, 192-, and 256-bit key lengths.
Two architectural versions are available to suit system requirements. The Standard version (KEXP-P) is more compact and is used with AES cores using a 32-bit datapath. The Fast version (KEXP-F) achieves higher throughput in conjunction with AES cores using a 128-bit datapath.
The KEXP core is a fully synchronous design and has been evaluated in a variety of technologies, and is available optimized for ASICs or FPGAs.
The KEXP is a highly integrated implementation of the AES key expansion. The input key is expanded and it can be used during encryption on the fly, without the need to store the whole key in a buffer.
During decryption, the expanded key needs to be fed backwards. This core can perform backward expansion on the fly without the need for an additional buffer.
Rising the input on the GO port triggers the beginning of the expansion of the KEY input.
The key size selection can be selected by the KSIZE input. Valid values for KSIZE are “00”, ”01” and “10” selecting 128, 192 or 256 bits respectively. The KSIZE inputs must not be changed while the data is processed.
The core then raises the KEY_REQ signal requesting the key. It then starts to expand the key according to the AES algorithm
During the expansion process, the expanded key data is available at the output KEY.
The expanded data is output in the correct order for use with AES cores during encryption.
At the end of the expansion operation, the signal KEY_LAST is raised. The core is immediately ready for another expansion operation and, in fact, the KEY_REQ signal is raised immediately after that.
Backward Key Expansion
During decryption, the expanded key must be fed to an AES core backwards. Backwards expansion works similarly to forward expansion and it is activated by raising the E_D input. Export Permits
This core implements encryption functions and as such it is subject to export control regulations. Export to your country may or may not require a special export license. Please contact CAST to determine what applies in your specific case.
The core has been verified through extensive synthesis, place and route and simulation runs. It has also been embedded in several products, and is proven in FPGA technologies.
Support
The core as delivered is warranted against defects for ninety days from purchase. Thirty days of phone and email technical support are included, starting with the first interaction. Additional maintenance and support options are available.
Deliverables
The core is available in ASIC (RTL) or FPGA (netlist) forms, and includes everything required for successful implementation. The ASIC version includes
- HDL RTL source
- Sophisticated HDL Testbench (self-checking)
- C Model & test vector generator
- Simulation script, vectors & expected results; synthesis script
- User documentation
The KEXP can be mapped to any ASIC technology. The following are sample pre-layout results reported from synthesis with a silicon vendor design kit under typical conditions, with all core I/Os assumed to be routed on-chip. The provided figures do not represent the higher speed or smaller area for the core. Please contact CAST to get characterization data for your target configuration and technology.
KEXP Standard Core ASIC Implementation Results
| ASIC Technology | Number of eq. gates | Fmax (MHz) |
|---|---|---|
| TSMC 7nm | 4,495 | 1,700 |
| TSMC 16nm | 5,393 | 1,600 |
| TSMC 28nm HPC | 6,134 | 500 |
KEXP Fast Core ASIC Implementation Results
| ASIC Technology | Number of eq. gates | Fmax (MHz) |
|---|---|---|
| TSMC 7nm | 9,192 | 1,600 |
| TSMC 16nm | 9,632 | 1,200 |
| TSMC 28nm HPC | 12,160 | 1,100 |
The KEXP can be mapped to any Altera FPGA device (provided sufficient silicon resources are available). The following are sample Altera results with all core I/Os assumed to be routed on-chip. The provided figures do not represent the higher speed or smaller area for the core. Please contact CAST to get characterization data for your target configuration and technology.
KEXP Standard Core Altera Implementation Results
| Family | Logic | RAM bits | Freq. (MHz) |
|---|---|---|---|
| Arria 10 GX (-2) | 456 ALMs | 0 | 100 |
| Stratix V (-1) | 426 ALMs | 0 | 150 |
| MAX 10 (-7) | 851 LEs | 0 | 100 |
KEXP Fast Core Altera Implementation Results
| Family | Logic | RAM bits | Freq. (MHz) |
|---|---|---|---|
| Arria 10 GX (-2) | 780 ALMs | 4,096 | 80 |
| Arria 10 GX (-2) | 827 ALMs | 0 | 80 |
| Stratix V (-1) | 754 ALMs | 4,096 | 100 |
| Stratix V (-1) | 825 ALMs | 0 | 100 |
| MAX 10 (-7) | 800 LEs | 4,096 | 50 |
| MAX 10 (-7) | 1,636 LEs | 0 | 50 |
The KEXP can be mapped to any AMD FPGA device (provided sufficient silicon resources are available). The following are sample AMD FPGA results with all core I/Os assumed to be routed on-chip. The provided figures do not represent the higher speed or smaller area for the core. Please contact CAST to get characterization data for your target configuration and technology.
KEXP Standard Core Xilinx Implementation Results
| Family | LUTs | BRAMs | Freq. (MHz) |
|---|---|---|---|
| Kintex 7 (-2) | 93 | 1 | 325 |
| Virtex 7 (-3) | 97 | 1 | 325 |
| Kintex UltraScale (-3) | 91 | 1 | 450 |
| Kintex UltraScale+ (-3) | 98 | 1 | 575 |
| Versal (-2) | 172 | 0 | 675 |
KEXP Fast Core Xilinx Implementation Results
| Family | LUTs | BRAMs | Freq. (MHz) |
|---|---|---|---|
| Kintex 7 (-3) | 581 | 1 | 250 |
| Virtex 7 (-3) | 579 | 1 | 250 |
| Kintex UltraScale (-3) | 580 | 1 | 325 |
| Kintex UltraScale+ (-3) | 580 | 1 | 425 |
| Versal (-2) | 603 | 1 | 300 |
Engineered by Ocean Logic.
Features List
- Satisfies Federal Information Processing Standard (FIPS) Publication 197 from the US National Institute of Standards and Technology (NIST)
- Employs user-programmable key size of 128, 192 or 256 bits
- Two architectural versions:
- Standard is more compact: 32-bit data path size
- Fast yields higher transmission rates: 128-bit data path
- Suitable for use with AES cores
- Simple, fully synchronous, reusable design
- Available as fully functional and synthesizable VHDL or Verilog, or as a netlist for popular programmable devices
- Complete deliverables include test benches, C model and test vector generator
Resources
AES Core Links
FIPS 197, Advanced Encryption Standard (AES): download PDF
AES test suite: The Advanced Encryption Standard Algorithm Validation Suite (AESAVS): download PDF